- Home
- About Us
- Recovery Services Individual RecoveryEnterprise RecoveryAdditional Recovery
- Software
- Testimonials
- Locations
Specialist data extraction tools for mobile phones and tablets
Chip-off and JTAG knowledge in mobile phone and flash data recovery is essential to ensure the highest success rates!
Chip-off and JTAG data recovery methods...
Mobile phone data recovery and all flash recoveries use two types of techniques. These offer data recovery engineers access to a low-level image of the data, by interrogating the NAND memory chip directly. However, both techniques are very different. Mobile phones, flash storage and solid-state-drives rely on memory chips for storing information in direct contrast to hard disk drives, which still use rotating platters and read/write heads.
Hard disk drives use a common approach to data storage, meaning that data recovery tools can be generic. Flash devices on the other hand vary considerably in their approach. With a wealth of different data formats, file structures, algorithms, memory types and configurations, data extractors are often ‘device specific’. This means that the only way to gain a bit for bit copy of the raw data is to interrogate the memory chips directly, effectively bypassing the operating system. This is where chip-off and JTAG technology features.
Keep your inbox safe from spammers!
Ever get fed up of constantly clearing your inbox to find that the very next day it is full of junk again?
Keep your inbox clean and safe…
It is easy to overlook your e-mail account and let it become crammed and unmanageable. Before long your inbox is full of unread messages, malware, spam and phishing emails. Whether you use an e-mail client such as Microsoft Outlook or a web-mail such as Gmail or Hotmail, an untidy inbox is a fantastic route for infections to attack your system. Before long you can become riddled with problems, which strain your system often to breaking point leading to data recovery problems. Data storage is cheap, but this is not about freeing up storage space. It is about keeping your system healthy.
Firstly you must understand that your email client is not a ‘to do’ list or a filing system, it is for communication. At Data Recovery Specialists we are asked to recover PST files more than any other file type. Generally this is because important information has been stored as attachments or in the body of e-mail messages. Recovering a PST file is only the start, a signature search is subsequently required to locate the necessary information which could be hidden in gigabytes of messages. Somewhat like looking for a needle in a haystack! So be sure to save important attachments or messages in your documents, rather than rely on an e-mail archive.
One attempt at data recovery
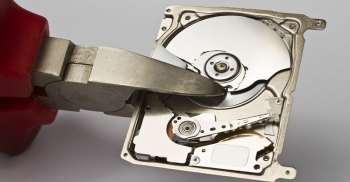
Depending on the type of problem with your hard drive, the user may well only have one attempt at data recovery so make sure you choose the right company! If your hard drive has failed mechanically, a skilled professional is going to rebuild that disk using donor parts. Data recovery after a logical failure can often be attempted many times without effecting the media at all. This is because the technician is not having to open the chassis for a mechanical or electronic repair.
Hard drives are precision instruments and are not designed to be disassembled. Similarly donor parts are often not compatible. To provide a quote for a data recovery and file listing of recoverable files, our experts have already rebuilt the hard drive and recovered the data. Where quotes are declined we will always return the media to its original condition and return to the client. Yet just the fact that the drive has been disassembled means a subsequent attempt at recovery will be more complicated.
Most hard drives these days have multiple platters. To remove platters a specialist extraction tool is required. Platters are aligned to very exact specifications. The tracks are packed so tightly that the actuator is unlikely to pick them up after the chassis is opened, even though the user may not have touched the spindle! Platter extraction is a very delicate procedure on any hard drives over 20Gb in size. Once the rotational alignment of the platters has been altered – even by a hundredth of a millimetre - the game is more or less over unless you are prepared to spend big bucks!
3 Permanent Ways To Erase Your Data
In our last blog,we discussed the importance of being able to securely and permanently erase end-of-life data.Whether you’re working for a company that has legal obligations to destroy customers’ personal information after a certain timeframe, or you’re looking to sell an old smartphone on eBay and want to make sure nobody digs up your selfies, it pays to know how to do the job properly. And yet this is often a source of confusion – lots of consumers and businesses hold misconceptions about what constitutes secure data destruction and what doesn’t.
Formatting a disk, for example, won’t actually wipe it – it just removes the existing file system and generates a new one, which is analogous to throwing out a library catalogue when you really want to clear out the library itself. What’s more, taking a hammer to your hard drives is no guarantee – however unlikely – that someone with enough time on their hands won’t be able to reassemble the platters and transcribe the data.
So, how can consumers and businesses achieve peace of mind that their sensitive information won’t be coming back to haunt them after it’s been deleted? There are actually a few different fail-safe data destruction methods that have the approval of international governments and standards agencies, which vary wildly in cost and come with their own particular advantages and disadvantages. Here are three of the most important.
Method 1: Data erasure software
One of the simplest ways to permanently erase data is to use software. Hard drives, flash storage devices and virtual environments can all be wiped without specialist hardware, and the software required ranges from free – such as the ‘shred’ command bundled with most Unix-like operating systems – to commercial products.
While different data destruction applications use different techniques, they all adhere to a single principle: overwrite the information stored on the medium with something else. So, a program might go over a hard drive sector by sector and swap every bit for a zero, or else with randomly generated data. In order to ensure that no trace of the original magnetic pattern remains, this is typically done multiple times – common algorithms include Scheier seven-pass, as well as the even more rigorous, 35-pass Gutmann method.
Unfortunately, there are a few drawbacks to software-based data erasure. For one, it’s fairly time-consuming. Then, perhaps more significantly, there’s the fact that if certain sectors of the hard drive become inaccessible via normal means, the application won’t be able to write to them. Nonetheless, it’ll be possible for someone with the right tools to recover data from a bad sector.
Obviously, software-based data erasure also hits a snag when you want to destroy information stored on media that can only be written to once, such as most optical discs.
VMware quietly updates virtualization backup and restore solution
VMware takes a bigger step into the backup and restore market for virtual machines with the latest release of VMware Data Recovery 1.1 (VDR)
VMware administrators may be interested and happy to know that VMware is finally offering a product to help with the burden of virtual machine backup and restore. The product is called VMware Data Recovery (VDR), and while it isn't exactly brand-new, VMware did recently update it to version 1.1, though without much fanfare.
Much like physical machines, there is a tremendous need out there to back up virtual machines. If a mission-critical virtual machine has a problem, you need a quick way to get it back up and running. Remember, virtual doesn't mean "problem-free."
While many people believe that VMware had already introduced a backup application prior to VDR, that just isn't the case. VMware did introduce VMware Consolidated Backup (VCB), and despite its name, it doesn't actually back up and restore anything. Instead, what it does is provide others with a mechanism to access the VMFS file system in order to back up and restore virtual machines. With VCB, administrators were able to either create custom scripts to perform backups or leverage third-party backup software from VMware partners.
How to repair a SQL Server 2005/2008 database in suspect mode
 This can happen following things like hardware failure, power outages, database files being locked by the Operating System (Anti-Virus, backup software etc.) or actual corruption of the database.
This can happen following things like hardware failure, power outages, database files being locked by the Operating System (Anti-Virus, backup software etc.) or actual corruption of the database.Attempting the repair procedure below is really a last resort. If you have good and recent backups, then if at all possible I would perform point-in-time recovery of the database concerned, as this emergency repair can (as the name suggests) result in data loss.
If you’ve gone through all of this like I once did though, and all other avenues failed, here are the steps that fixed it for me:
EXEC sp_resetstatus 'YourDBName'
ALTER DATABASE 'YourDBName' SET EMERGENCY
(You won’t be able to query the database until it’s in EMERGENCY mode!)
DBCC CHECKDB ('YourDBName')
ALTER DATABASE YourDBName SET SINGLE_USER WITH ROLLBACK IMMEDIATE
DBCC CHECKDB ('YourDBName') WITH NO_INFOMSGS, ALL_ERRORMSGS
DBCC CHECKDB ('YourDBName', REPAIR_ALLOW_DATA_LOSS)
ALTER DATABASE YourDBName SET MULTI_USER
In the end, I just had to rebuild a couple of indexes after the repair process and everything was recovered….phew!
ALTER INDEX ALL ON [YourTableName] REBUILD
Again, it’s worth stressing that this is a last resort – use a good backup/standby etc. first, if you have one! Copyright © 2026 DataRecoup Recovery Services. All Rights Reserved. Designed by DataRecoup Lab.